Hacking naked Akamai ARL at scale
Update 2021-08-06 : An Akamai notice [backup] posted some months after our publication suggests this ARL issue will stop working globally 2021-08-10. They also wrote an explicit vuln explainer. [gated link] Companion repo and links have been updated to reflect this sunset.
Akamai is the effective edge of many big organizations.
Many big organizations have an unruly amount of domain space — maybe they don’t even know how many subdomains are out there.
When you can’t keep track of that, sometimes you take down real content without notifying the right people and/or cleaning up.
Take that group and overlap it with the Akamai people, you’ve got yourself our target group of the day. 🤤
We are looking for abandoned subdomains that give us a “naked” look at Akamai. This makes them susceptible to loading whatever content from other Akamai sites that we want.
Realistically, an attacker could load up phishing content or other evil stuff.
In a bug bounty context, you might get away with just reflected cross-site scripting off some old Akamai site somewhere.
A susceptible target looks like this below —

And let’s take a closer look at the response —
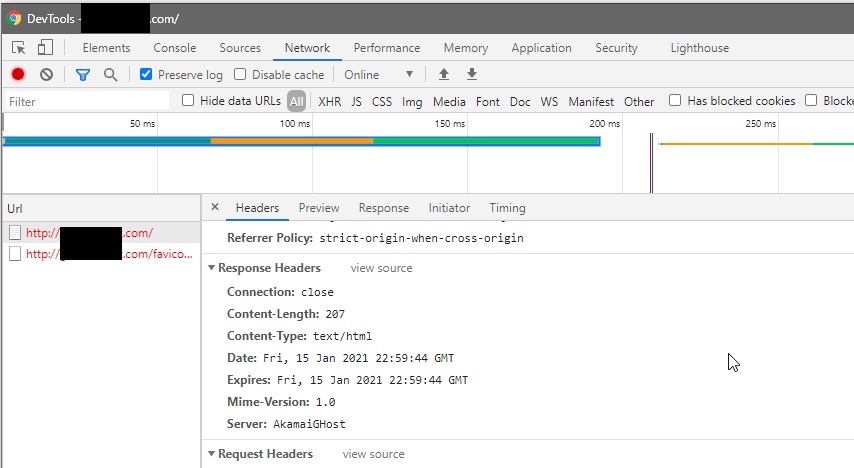
Got something that looks like that? Then we can progress to an actual payload in step 2.
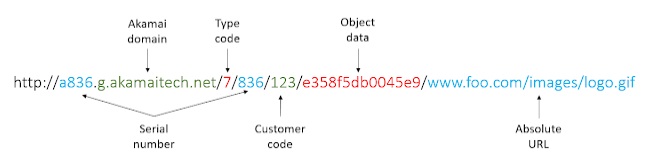
This requires a bit of ARL knowledge (or go steal my GitHub repo). Let us credit Akamai for documenting.
I don’t want to draw too much attention to the XSS vulnerable site so won’t go over this in detail. But successfully scripting an exploitation test should assess response headers and content, obviously.
After seeing this all come together firsthand once, I set out to do it “at scale”.
Some industrious folks or Big Data engineers will laugh at my use of “at scale” to try just over 2,000 targets but whatever!
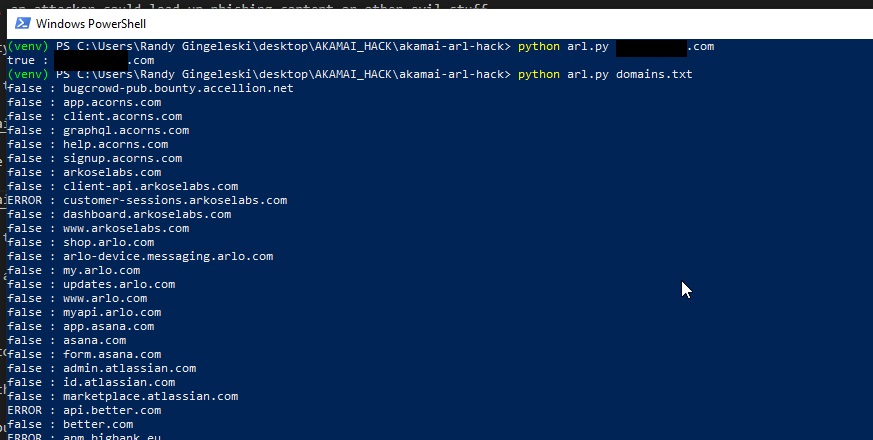
A repo of the work came out like this —
https://github.com/war-and-code/akamai-arl-hack
My Python script accepts a line-delimited target list or one-off entries. I grabbed arkadity/bounty-targets-data off GitHub and leveraged its domains.txt with 2,259 entries.
“Did you get any hits?”
I wouldn’t want to give them away, but will have beaten you to the bounty queue in such a case.
Try this all out for yourself — happy hacking! 👽✌
Randy Gingeleski - GitHub - gingeleski.com - LinkedIn