How to identify in-client bot detection
Walking through how to clock 4 in-client bot detectors like Google reCAPTCHA and Akamai Bot Management SDK.
Scenario 1 - you are a person who writes bots (or OpenBullet configs or whatever) to yield 40,000 U.S. dollars per year that you live on.
Scenario 2 - you are an in-house security person who is trying to tell whether bot detection stuff the client team was supposed to put in actually went in.
In this post, we identify the presence of in-client bot detectors by just firing some JavaScript in the ol’ dev tools console.
- Google reCAPTCHA
- Akamai Bot Management SDK
- WhiteOps
- Shape Security
These are the big players in the space. They’re recording telemetry and doing fingerprinting in your browser. It has got to be done with JavaScript, and therefore we can snuff out their presence with more JavaScript.
Google reCAPTCHA
The easiest way to see this guy is to just open the Sources developer tool instead of Console.
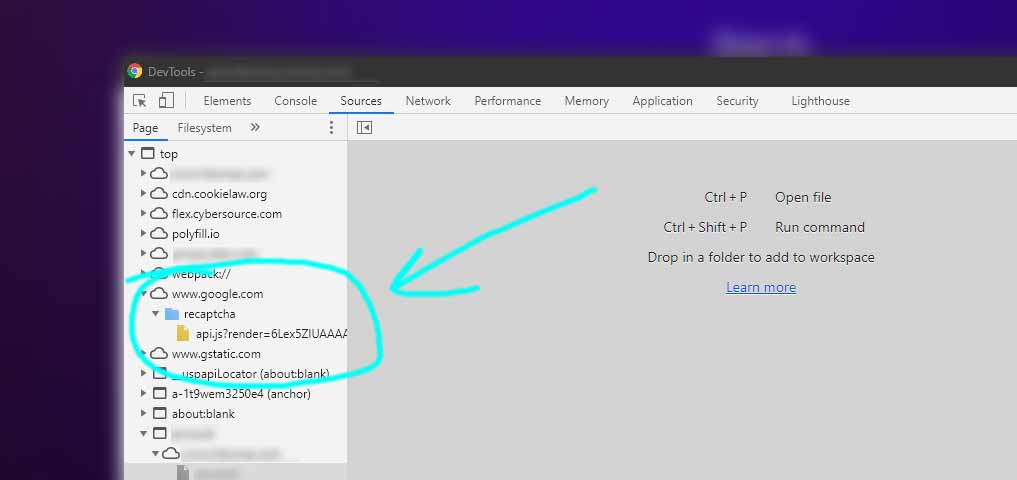
Per the official installation instructions, users of reCAPTCHA – version 2, version 3, I don’t care – include the following.
<script src="https://www.google.com/recaptcha/api.js"></script>
If you’re really disappointed we’re not finding it with JS, then fine, we’ll go that way. Execute the following.
console.log(typeof grecaptcha !== 'undefined' && typeof grecaptcha.ready !== 'undefined')
The object that’s watching you screw around on the page is grecaptcha and I threw in a function check just to avoid the most basic of fake-outs.

Try it on Google’s own demo form.
Akamai Bot Management SDK
This one’s a little tricker because often it gets injected by Akamai WAF itself. Magic!
What gets injected? At the time of this writing, it’s this bmak object.
> console.log(bmak.get_telemetry())
7a74G7m23Vrp0o5c9198171.64-1,2,-94,-100,Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.102 Safari/537.36,uaend,12147,20030107,en-US,Gecko,3,0,0,0,393816,9227162,1920,1040,1920,1080,1904,952,1920,,cpen:0,i1:0,dm:0,cwen:0,non:1,opc:0,fc:0,sc:0,wrc:1,isc:0,vib:1,bat:1,x11:0,x12:1,8321,0.297870101148,800284613581,0,loc:-1,2,-94,-101,do_en,dm_en,t_en-
...
So if we’re going to straighten that out into a detection script, you might take this below.
console.log(typeof bmak !== 'undefined' && typeof bmak.get_telemetry !== 'undefined')
Akamai doesn’t provide a test form but at the time of this writing you can try https://vitacost.com/MyAccount/Login.aspx.
WhiteOps
Okay – I haven’t been able to reliably locate WhiteOps in the wild to write JavaScript for this.
It seemed apt to include them as one of the older players in this space. They were also a stop on my 2019 job interview tour.
Reddit is one place I went looking for it. See the following accounts from someone who observed WhiteOps there a few months ago.
- https://smitop.com/post/reddit-whiteops/
- https://smitop.com/post/whiteops-data/
- https://smitop.com/whiteops-main.js
No dice for me though.
Some domains that may indicate the presence of WhiteOps –
adxyield.com
adzmath.com
whiteops.com
Some indicators for scripts –
*ozoki_tc
*ozoki_os
*ozoki_url
*ozoki_ct
||ozoki_opt
*ozoki_loaded
*ozoki_call
Shape Security
My understanding is that Shape does some inject-o voodoo like Akamai BotMan too.
But, there’s some additional stuff going on that makes them the most cryptic product here.
- Sensor data is encoded with Superpack
- Superpack-encoded data is encrypted using a custom function
- Encrypted data is Base64-encoded but the standard Base64 alphabet is shuffled (!!)
What does that mean for our JavaScript? It’s a royal pain in the ass and I’m not trying to script that.
Instead we’ll learn the other telltale signs from the developer tools still.
One check you can try by just viewing page source is Ctrl+F for blackfish.
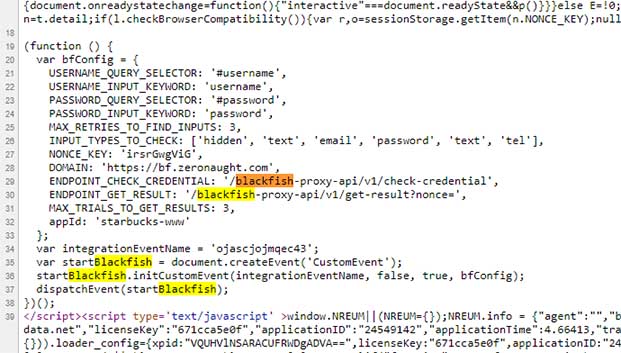
This is another Shape product that checks credentials for a risk score. It’s commonly in use on bot-prone endpoints.
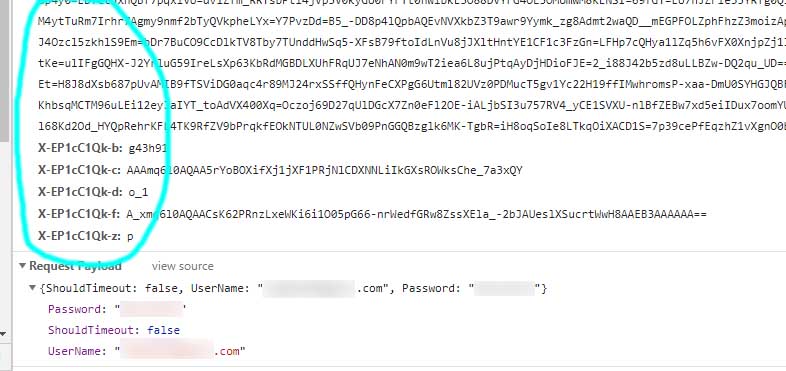
The other, more reliable check is to eyeball the headers like the following on your login request. Run the network tool to record your login form submission.
x-XXXXXXXX-a
x-XXXXXXXX-b
x-XXXXXXXX-c
x-XXXXXXXX-d
x-XXXXXXXX-f
x-XXXXXXXX-z
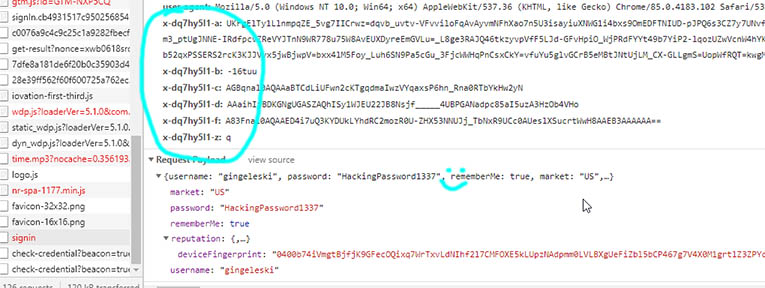
See the uppercase X’s in my code block will change depending on the target. Here’s another website below.
Shape doesn’t provide a test form either but you can try https://www.starbucks.com/account/signin or https://www.chipotle.com/order/sign-in.
If you’re trying to attack the bot detector then I’ll suggest the below GitHub repo as a starting point.
https://github.com/sonya75/starbucks-botdetection-cracked
Closing thoughts
If these kind of detection tricks were out there already, I hadn’t seen them all grouped succinctly like this on the clear web. Shrug.
Obviously there is a server-side expectation of telemetry strings from these things. That’s why we are detecting here.
Go find an easier target in these cases. Ripping the stuff out or overriding their outputs is pointless.
Happy hacking/botting. 💻
Randy Gingeleski - GitHub - gingeleski.com - LinkedIn